Online lesson module - A practical walk through First Amendment foundations, controversial but protected expressions, categories of unprotected speech, and contemporary questions of platform power, VPNs, and the Tor network. This lesson follows our in‑class slide deck and uses the same conceptual scaffolding for continuity.
Table of Contents |

1) Free Expression: Constitutional and Global Frames
The First Amendment of the Constitution articulates a bright‑line commitment: “Congress shall make no law … abridging the freedom of speech, or of the press.” [1]
Interpretive anchor: Political and religious speech receive the highest protection under the US constitutional framework. Restrictions must satisfy content‑neutral “time, place, and manner” standards and leave open alternative channels of communication. [2]
Universal Declaration of Human Rights, Art. 19
Everyone has the right to seek, receive, and impart information and ideas through any media and regardless of frontiers. This is the global lingua franca of communication rights.[4]
2) Free Expression in American History
The First Amendment’s promise of free expression has never fully insulated the United States from attempts to silence dissenting voices or control the press. A vivid early example came in 1798, when the Federalist-controlled Congress enacted the Alien and Sedition Acts, a series of laws designed to suppress opposition during a time of political and international tension. The Sedition Act, in particular, made it a crime to “write, publish, or print any false, scandalous, and malicious writing” against the president, Congress, or the federal government.[7]In practice, these laws targeted journalists, editors, and immigrant supporters of the Democratic-Republican Party, whose criticism of Federalist policies was reframed as a threat to national security. The Acts proved deeply unpopular, provoking a national backlash over what many viewed as an assault on constitutional liberties. When the Federalists were voted out of power in 1800, the new administration swiftly allowed the legislation to expire, marking an early and decisive reaffirmation that political dissent and criticism of public officials lie at the core of the American free speech tradition. [8]
2.1 Prior Restraint and its Discontents
Prior restraint refers to government actions that prevent speech or publication before it occurs, typically through injunctions, licensing, or other forms of preemptive censorship. Prior restraint has deep roots in English common law, where monarchs required the press to obtain royal licenses, in effect silencing political or religious dissent. [9]The struggle over prior restraint became especially visible in twentieth-century American jurisprudence, as courts were forced to define the limits of government control over publication. In 1931, the Supreme Court’s decision in Near v. Minnesota marked the first major ruling to strike down a state’s attempt to suppress a newspaper before distribution. The case arose when Minnesota officials tried to shut down The Saturday Press for accusing local politicians of corruption. The Court ruled that such pre-publication censorship violated the First Amendment, establishing that punishment for libel or incitement must come after publication through due process, not before. [10]
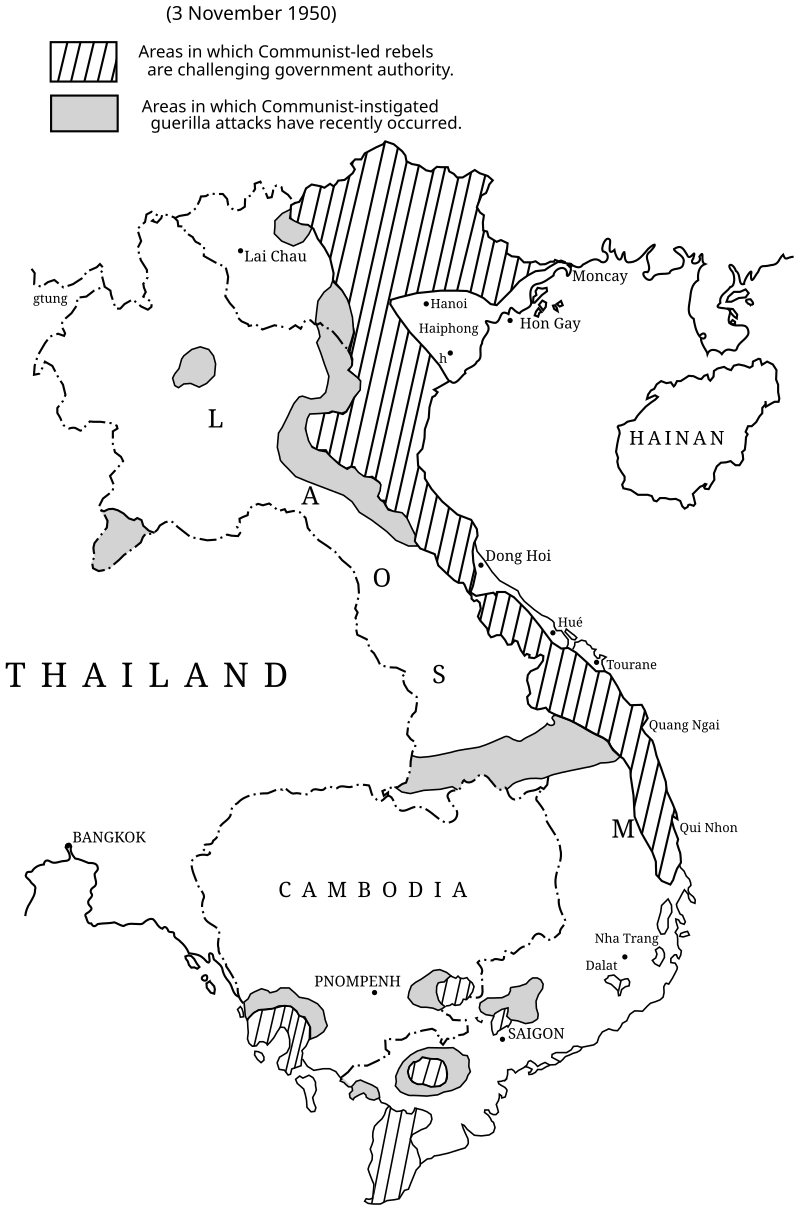
|
Four decades later, in 1971, New York Times Co. v. United States—the “Pentagon Papers” case—reaffirmed that even claims of national security rarely justify silencing the press in advance. The Nixon administration’s effort to block the Times and Washington Post from publishing leaked documents on the Vietnam War was rejected, with Justice Black famously writing that “the press was to serve the governed, not the governors.” [11]
The issue of prior restraint resurfaced in 1979 with United States v. The Progressive, when the Department of Energy (DOE) sought to prevent The Progressive magazine from publishing an article titled “The H-Bomb Secret: How We Got It, Why We’re Telling It.” Written by freelance journalist Howard Morland, the piece compiled publicly available scientific information to explain the general principles of hydrogen bomb design.
The US government argued that even though the H-bomb data was unclassified, the article could help hostile nations develop nuclear weapons and therefore threatened US national security. A federal judge initially granted an injunction, marking one of the rare instances in U.S. history where prior restraint was temporarily upheld. However, the case was dropped before reaching the Supreme Court after similar information appeared in other publications, rendering the injunction moot. [12]
3) One Man’s Vulgarity is Another’s Lyric
For instance, most false statements (or the “right to lie”) are protected as long as they do not amount to defamation, perjury, or professional malpractice. The Supreme Court made this point explicit in United States v. Alvarez (2012), when it struck down the Stolen Valor Act, which had criminalized falsely claiming military honors. The Court reasoned that the government cannot impose blanket bans on lies without threatening the broader freedom to engage in activities intrinsic to public discourse and self-expression. [13]
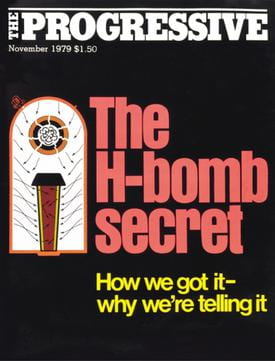
Source: By The Progressive magazine, Fair use, https://en.wikipedia.org/w/index.php?curid=20156806
Another recurring controversy involves the publication of classified or sensitive government information by journalists or private citizens. In most circumstances, the First Amendment prohibits the government from punishing the press for publishing lawfully obtained materials, even if those materials expose state secrets or political wrongdoing.
The Pentagon Papers case (1971) and the United States v. Progressive “H-bomb” case (1979) we’ve discussed earlier reaffirmed this principle, holding that the risk of embarrassment or diplomatic tension generally does not outweigh the public’s right to know.
4) Unprotected Speech
While the First Amendment offers broad protection for expression, it is not absolute. Over time, the US Supreme Court has defined a narrow set of unprotected categories of speech—forms of expression that are considered so harmful, fraudulent, or devoid of public value that they do not merit constitutional protection. Each category has been shaped by specific historical cases, reflecting the tension between liberty and harm prevention in a democratic society.4.1 Defamation (libel & slander)
Defamation refers to false statements of fact that unjustly harm another person’s reputation. For speech to qualify as defamation, it must meet ALL four criteria: it must be:(1) Untrue - verified to be factually false or misleading.
(2) Public - cannot be an one-on-one private conversation, must be at minimum communicated to a third party individual.
(3). Actual Malice - made with reckless disregard for truth AND the intent to cause harm.
(4)Actual Injury - must result in verifiable monetary or reputational damages [15]
Although The Onion’s June 6, 2025 article, “IRS Allows Taxpayers To Deposit Payments Directly Into Elon Musk’s Bank Account,” makes numerous false claims about the U.S. government and Elon Musk, it is a work of satire and does not meet the legal criteria for defamation. Satirical and parodic works like The Onion’s are protected precisely because they cannot reasonably be understood as stating actual facts. The publication made clear signals to its readers that the piece is humorous commentary on systemic wealth inequality, not actual news report. [16]
|
4.2 Fighting Words (rarely applicable today)
The category of fighting words refers to a very narrow class of speech acts so personally abusive and confrontational that they are likely to provoke an immediate violent response from the person addressed. The doctrine was first articulated in the controversial case Chaplinsky v. New Hampshire (1942). Since then, courts have dramatically narrowed the fighting words doctrine, and it is almost never applied today—surviving more as a historical artifact. [17]To qualify as fighting words, speech must satisfy ALL of the following elements:
(1) Personally Abusive — must be directed at a specific individual in a way that is extremely insulting or demeaning;
(2) Face-to-Face — must occur in a close, personal encounter where physical confrontation between involved parties is possible;
(3) Incite Immediate Physical Violence — the speech must be so severe where an reasonable be provoked into immediate physical retaliation (not merely offend, disturb, or anger).
(4) Lack of Broader Value — must exist purely as a personal insult and cannot be reasonably interpreted as having serious literary, artistic, political, or scientific value (“SLAPS” value)
A work is considered obscene only if it satisfies ALL of the following elements (also known as the Miller’s test):
(1) Appeals to the Prurient Interest - That “the average person, applying contemporary community standards,” would find that the work, taken as a whole, appeals to an excessive or unhealthy interest in sexual matters. [19]
(2) Patently Offensive - Whether the work depicts or describes patently offensive "'hard core' sexual conduct specifically defined by the regulating state law, as written or construed." [20]
(3) No "SLAPS" Value - the work, taken as a whole, does not have serious literary, artistic, political, or scientific value (“SLAPS” value). [21]
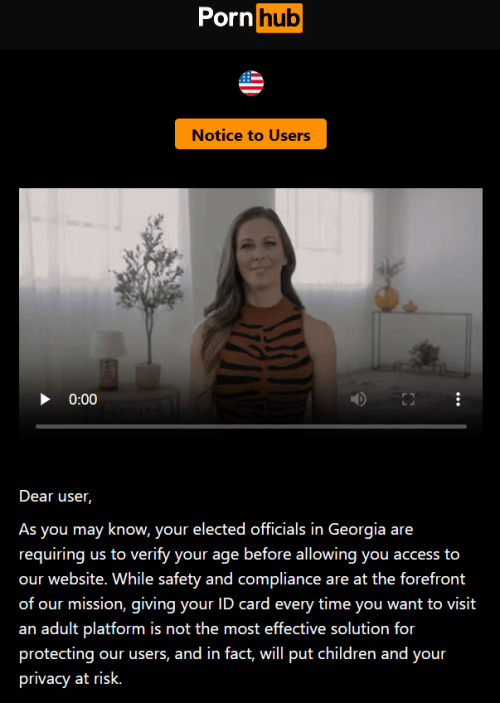
Age Verification Laws and Digital Rights Under the Miller's test, most mainstream online pornography platforms are not likely to meet the legal definition of obscenity. The Miller framework narrowly defines obscenity as expression that appeals to prurient interests, depicts sexual conduct in a patently offensive way, and lacks serious literary, artistic, political, or scientific value. By contrast, U.S. courts have repeatedly held that consensual adult pornography constitutes protected speech (so long as it does not involve minors or non-consensual acts), as they may reasonably be understood as having some expressive or artistic value. [22] However, beginning around 2021, a global wave of adult-content removals and site-access restrictions emerged—not through direct governmental censorship, but via indirect enforcement mechanisms. Rather than invoking obscenity law, public authorities and private intermediaries have increasingly relied on trafficking and age-verification statutes to limit access to online adult material. These include 18 U.S.C. §§ 2257 and 2257A, which mandate age and identity verification for all performers in sexually explicit content, and the FOSTA–SESTA package (2018), which expanded platform liability for facilitating sex trafficking or prostitution. [23] Under the threat of severe financial and legal penalties, credit card companies and payment processors suspended services to adult-content platforms such as Pornhub until they implemented stricter user identity and age verification systems that satisfied government and corporate compliance standards. This strategy effectively bypasses traditional obscenity law, achieving de facto regulation through economic pressure and private enforcement rather than court rulings. Many digital rights and free expression advocates have voiced concern that such measures, while intended to prevent exploitation, expand the infrastructure for online censorship and erode user privacy. Mandatory age-verification systems require users to upload sensitive identification documents, increasing the risk of data breaches, identity theft, and potential state surveillance. In this way, the contemporary regulation of adult content reflects a shift from moral censorship under obscenity doctrine to a new regime of bureaucratic and corporate gatekeeping, where privacy and free expression are increasingly contingent on compliance with opaque verification systems. [24] |
4.4 Intellectual Property Violations
While the First Amendment protects expression, it does not protect the unauthorized use of another person’s creative work. Copyright infringement is one of the most common forms of restricted speech in the digital age. In fact, the vast majority of online takedown and censorship cases involve intellectual property violations, not hate speech or political dissent.
Under U.S. law, copyright protection extends for the lifetime of the author plus 70 years after their death, a duration considerably longer than in most other countries. Once that period expires, the work enters the public domain, where it may be freely used, adapted, or redistributed.
However, a significant loophole allows corporations to preserve their intellectual monopolies: by continually producing “new” versions or derivative works based on existing characters and franchises. Each new iteration—whether a sequel, prequel, or cinematic remake—resets the clock on copyright protection for that specific creative expression. This system contributes to the recent wave of live-action remakes, reboots, and remasters of older works in film and television. [25]
4.5 Speech Integral to Criminal Conduct
The final major category of unprotected speech encompasses expressions that are themselves integral to criminal activity. Unlike controversial or offensive ideas—which remain protected under the First Amendment—these forms of communication are inseparable from the commission of a crime. The law draws a firm line between speech that expresses an idea and speech that acts as a mechanism of harm.
Examples include fraud and scams, where deceptive speech is used to obtain money or property through misrepresentation; the possession and distribution of child abuse material, which is categorically excluded from protection because it involves the documentation of real criminal abuse; criminal solicitation or conspiracy, in which language functions as the coordination or encouragement of illegal acts; and targeted harassment or threats of specific, imminent harm, where speech directly endangers the safety of an identifiable person.
In the digital age, many of these offenses increasingly manifest as forms of cybercrime—where speech itself becomes both the medium and mechanism of violence. [26]
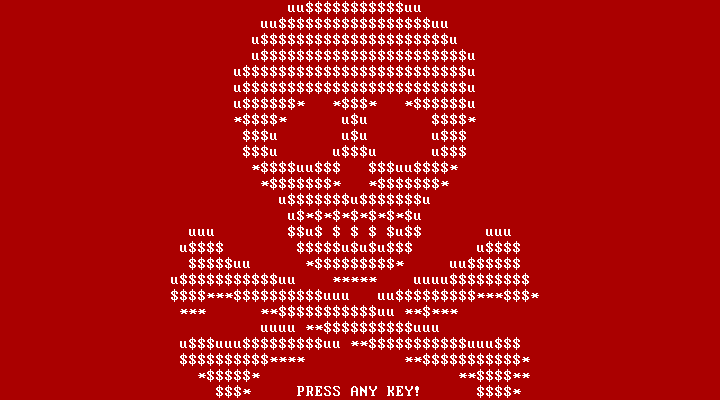
An example illustrating this boundary is the case of Petya, a family of ransomware first identified in 2016. Petya malware encrypts the victim’s hard drive and prevents their computer from booting, displaying a ransom note demanding payment in cryptocurrency (such as Bitcoin) to restore access. [27]
5) Internet Censorship & Communication Rights
As discussed in our previous lesson, the internet remains an enduring paradox: it is both an infrastructure of free expression and a technology of control. On one level, it has democratized access to speech and empowered individuals to publish, organize, and collaborate across geographic and political boundaries. Yet the same architecture that enables open exchange also provides governments and corporations with unparalleled capacities for surveillance, behavioral manipulation, and information restriction. In this way, the internet operates simultaneously as a public sphere and a system of governance—a space where freedom and regulation constantly collide.
Forms of Internet Censorship:Content Blocking: when Internet Service Providers (ISPs) or regulatory agencies restrict access to certain websites, social media platforms, or news outlets—often justified in the name of national security or “public morality.” [28] Surveillance & Data Harvesting: allow both states and private firms to monitor user activity, constructing detailed behavioral profiles that can be used to shape, predict, remove, or "shadow ban" speech.[29] Algorithmic Filtering: Platforms algorithmically curate or suppress visibility of particular content, can be driven by the economic logic of engagement or government pressure.[30] Legal/Administrative Pressure: Arrests, fines, or online takedown orders targeting journalists, activists, users, ISPs, sites and payment processors. |
In response to these pressures, scholars and civil society groups have advanced the framework of communication rights, extending the logic of free speech into the digital age. These rights include:
| The right to information - freedom to seek, receive, and impart information through any media (UN Declaration of Human Rights, Art. 19).
The right to equitable digital access - free from discriminatory throttling or commercial gatekeeping.
Freedom from surveillance - protection from arbitrary surveillance and content restriction. Data privacy - protection of personal data from being collected and used without user’s authorization. |
Together, these principles reflect the spirit of Article 19 of the Universal Declaration of Human Rights (1948), which recognizes that the ability to communicate “through any media and regardless of frontiers” is essential to both human dignity and democratic governance. [31]
The persistent balancing problem for communication rights lies in reconciling legitimate security concerns with the preservation of user rights protections. Measures enacted under the guise of protecting citizens (e.g. to combat terrorism, misinformation, or cybercrime) can easily evolve into permanent instruments of control. Once extraordinary powers are normalized, they seldom retreat. Thus, maintaining an open and pluralistic internet requires institutional transparency, public oversight, and digital literacy to ensure that digital protections do not quietly become digital censorship. [32]
5.1 VPNs: Benefits and Constraints
A Virtual Private Network (VPN) is a tool that encrypts a user’s internet traffic and routes it through a remote server, effectively masking the user’s IP address and geographic location. In doing so, VPNs provide a degree of privacy and autonomy in digital communication, which can be vital for journalists, activists, or citizens in countries with heavy online surveillance.
From a free speech perspective, VPNs extend the practical reach of expression by allowing individuals to bypass censorship, access restricted information, and protect their anonymity while engaging in political or social discourse. However, while VPNs are often marketed as instruments of digital freedom, they also introduce new ethical, legal, and trust-based dilemmas.
Why users adopt VPNsMask IP location to reduce tracking and profiling by advertisers, governments, or hostile actors. Limit ISP and search engine data collection, preventing providers from logging browsing histories. Bypass censorship and geo-restricted content, such as blocked news sites or streaming services. Mitigate dynamic pricing based on a user’s location, device, or browsing history. Secure, nonprofit optionsMost commercial VPNs operate under opaque ownership structures, and many “free” VPNs monetize user data through surveillance advertising or analytics resale. By contrast, a small number of nonprofit projects are designed explicitly to serve privacy and anti-censorship goals:
Constraints and Ethical Implications
|
5.2 The Tor Network and the “Dark Web”
Source: Tor Project. Mobile Tor Manual. Last modified 2024. https://iacobus.pages.torproject.net/manual/ca/mobile-tor/ Whereas a VPN relies on a single provider to encrypt and reroute traffic, Tor (also known as the Onion Router) -- an open source, open access project -- distributes this process across a decentralized network of volunteer-run servers, or “relays.” As data travels through multiple nodes, each layer of encryption is peeled away like an onion, ensuring that no single relay knows both who the user is and what content they are accessing. This structure minimizes centralized control and makes it exceptionally difficult for surveillance systems to trace communication back to its origin. [33] Tor serves as both a technical safeguard for privacy and a philosophical statement about informational freedom. For users in heavily censored environments, Tor can mean the difference between silence and participation. Yet Tor’s very strength—its multilayered anonymity—also fuels public suspicion. The same system that protects dissidents and reporters can be used by criminals to conduct illicit trade, distribute malware, or traffic in stolen data. |
Advantages of using TorCircumvent Censorship: Enables users in restrictive regimes to access blocked sites and communication tools. Protect Privacy: conceals both user identity & browsing activity from ISPs, governments, and advertisers. Digital Democracy: Tor Project is open-source and community-run. Journalists, activists, and whistleblowers use it to safely share information without fear of retaliation. |
Constraints & Ethical ConcernsTor can be slow due to multiple encryption layers and limited volunteer bandwidth. While Tor safeguards legitimate users, it is also exploited for cybercrimes such as illegal marketplaces Just like the VPNs, access to Tor is also heavily restricted in many countries. |
References
|